Agencies with mission-critical systems used by dispatch, records, and field operations
Law Enforcement IT & Security
Law Enforcement
We help law enforcement teams strengthen operational reliability, secure role-based access, and execute incident response workflows with clear accountability.

Industry detail
Ideal business profile
The kinds of teams and environments this page is built for.
Teams requiring strict access controls across role-sensitive data workflows
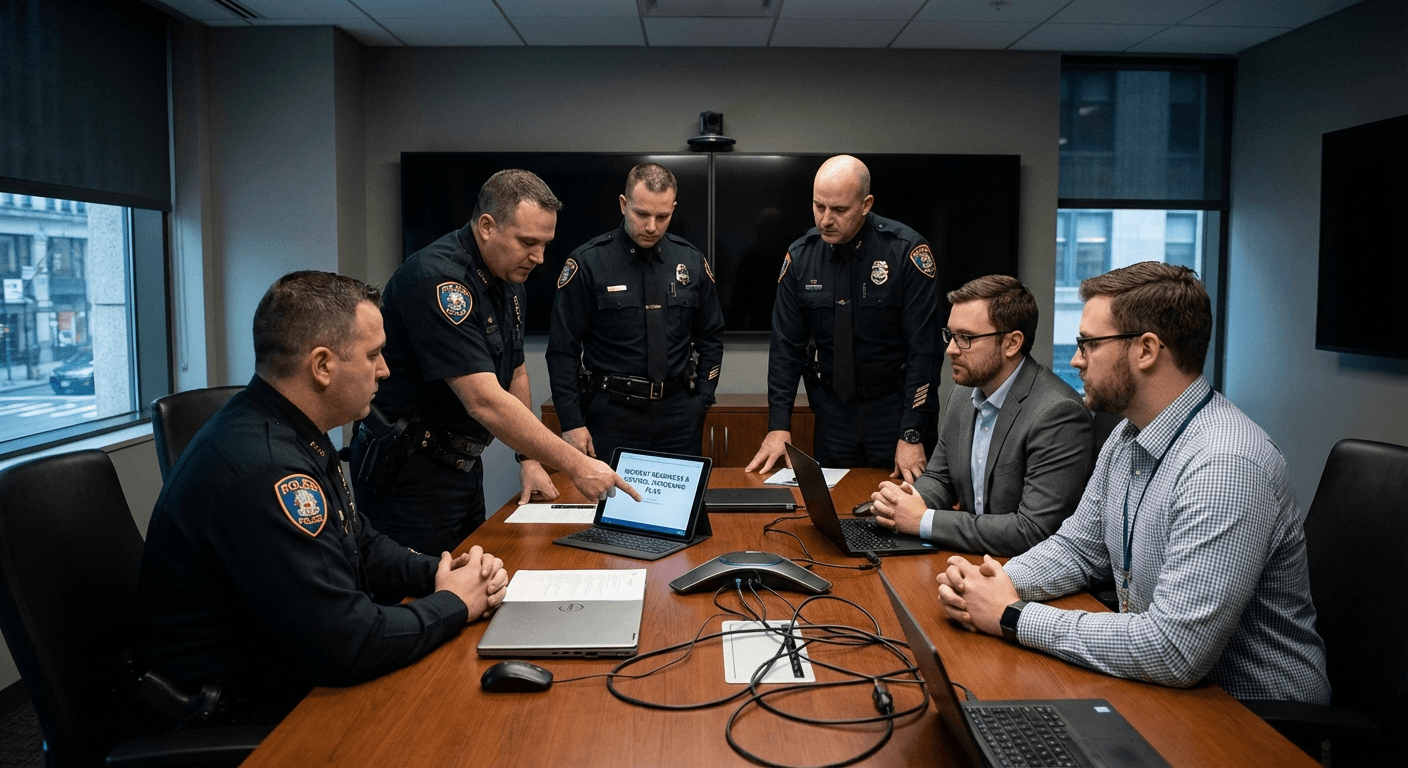
Organizations seeking stronger coordination between IT, leadership, and operations
Leaders prioritizing defensible response procedures and continuity planning
Industry detail
Operational environment
What day-to-day operations usually look like in this vertical.
Operational technology spans dispatch support, records platforms, and agency communications
Access models must align tightly to role responsibilities and policy expectations
System unavailability can disrupt time-sensitive field coordination
Legacy dependencies and vendor integrations create mixed risk profiles
Incident triage quality is heavily dependent on clear command ownership
Industry detail
Typical system dependencies
How daily work, handoffs, and technical dependencies usually line up.
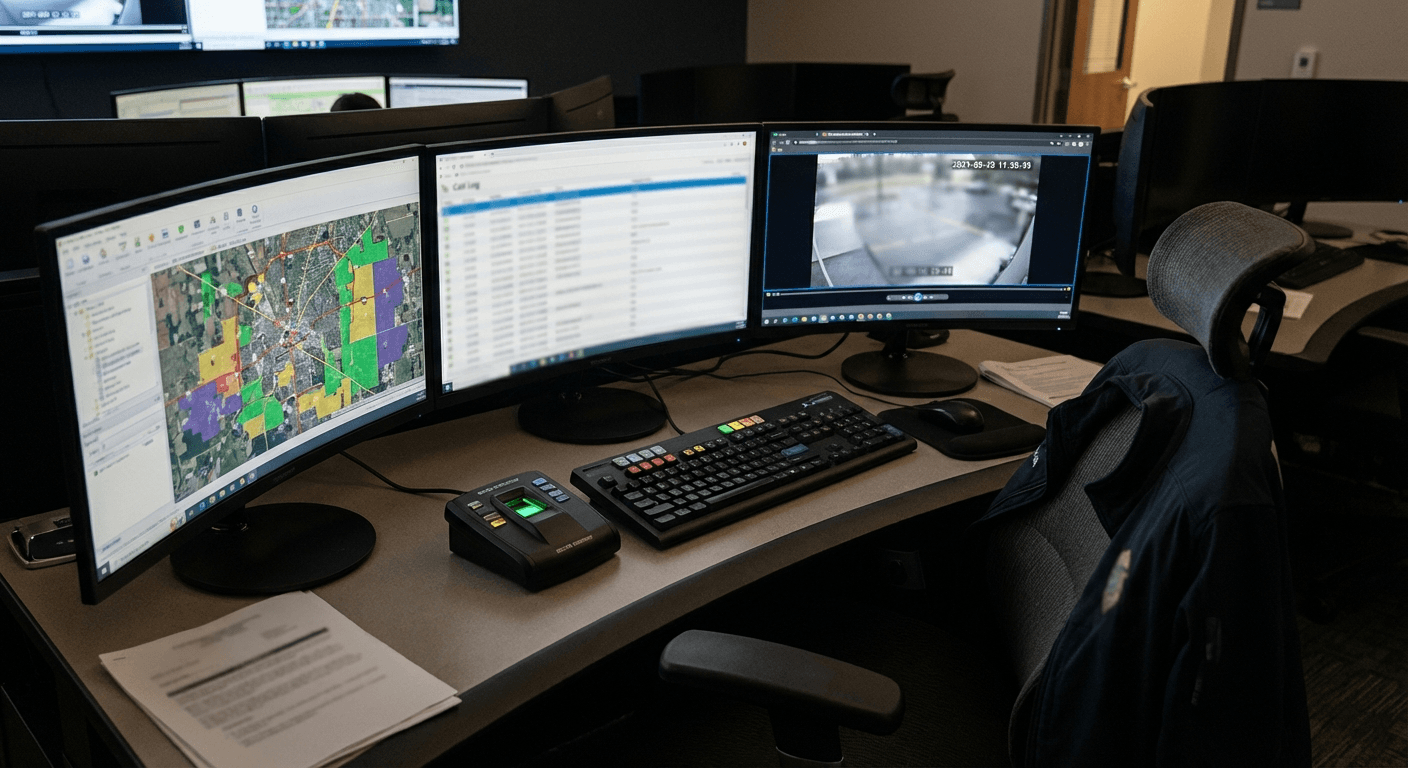
Systems and handoffs that shape support priorities
Use this view to connect technical recommendations to the way the team actually works.
Industry detail
Core pain points
The recurring issues that usually create stress, exposure, or operational drag.
Operational disruption during high-demand incident windows
Complex access governance across teams and sensitive data domains
Delayed triage due to fragmented visibility and escalation paths
Inconsistent endpoint hardening across agency environments
Limited capacity to execute proactive resilience improvements
Industry detail
Risk realities
Where threats and fragility tend to concentrate for this type of organization.
Authentication failures or misuse can expose sensitive operational workflows
System outages can directly affect mission execution and coordination speed
Incomplete incident documentation increases post-event recovery friction
Vendor dependency risk can amplify incident impact when fallback plans are weak
Industry detail
Compliance context
Frameworks and regulatory obligations that shape priorities in this sector.
CJIS Security Policy
Agencies handling criminal justice information need rigorous controls for access, auditing, and security operations.
How Blueforce applies it: We align control implementation with role boundaries, audit-ready practices, and operational continuity requirements.
NIST CSF / Incident Lifecycle Guidance
Sustained readiness requires continuous governance, detection, response, and recovery discipline.
How Blueforce applies it: We build repeatable response workflows and accountability checkpoints into daily operations.
CISA Operational Readiness Practices
Organizations should prioritize practical controls and response capability that can execute under pressure.
How Blueforce applies it: We sequence work around high-impact controls and validated response drills.
Industry detail
Service mapping
How Blueforce services map into the actual needs of this environment.
Primary track
Managed IT & Cybersecurity Foundation
Harden mission-critical systems and establish disciplined, role-owned incident execution.
- • Critical-system dependency map and priority support coverage
- • Role-specific identity and access-control hardening
- • Endpoint policy standardization with remediation governance
- • Incident runbooks with operational command and communication paths
Expansion track
AI & Context Operations Expansion
Improve operational throughput for non-sensitive coordination workflows once core controls are stable.
- • Context-aware triage for internal support and operational queues
- • Automation for repetitive administrative and status workflows
- • Operational telemetry dashboards for response indicators
- • Governance controls for constrained, role-safe automation adoption
Industry detail
30 / 60 / 90 roadmap
A practical phased sequence for stabilizing the environment.
Days 1-30
Stabilize mission-critical operations and command ownership.
- • Map mission systems and high-impact dependency paths
- • Define incident authority, communications, and escalation chain
- • Close urgent access and endpoint weaknesses
- • Set baseline reporting for leadership and operational stakeholders
Days 31-60
Normalize hardened controls and response drills.
- • Standardize remediation cadence and exception decisions
- • Implement refined role-based access patterns
- • Run incident simulations tied to agency-critical scenarios
- • Improve vendor escalation playbooks for shared dependencies
Days 61-90
Scale readiness and continuous improvement loops.
- • Tune alerts, handoffs, and triage timing
- • Introduce targeted automation for low-risk operational friction
- • Formalize recurring control and readiness reviews
- • Refresh execution roadmap using operational incident insights
Industry detail
Priority support path
The work needs clear ownership, timing, and follow-through.
Support rhythm that matches the team
Each phase needs ownership, sequencing, and a support model that fits the way work gets done.
Industry detail
Priority controls checklist
The controls and process disciplines most often worth addressing first.
Map systems with direct mission execution dependency
Enforce role-based access boundaries and periodic review
Standardize endpoint controls and remediation tracking
Document incident command decisions and communication templates
Validate backup and recovery ownership responsibilities
Establish vendor escalation response timing expectations
Run recurring mission-impact scenario drills
Maintain leadership visibility into unresolved high-risk items
Industry detail
Scenario playbooks
Examples of the kinds of situations this environment needs to be ready for.
Dispatch-Support System Degradation
Trigger: Critical support system performance drops during active operational demand.
First response: Activate high-priority command workflow, isolate affected service boundaries, and execute continuity protocol.
Stabilization: Restore essential functionality, reconcile delayed workflows, and harden recurrence controls.
Unauthorized Access Attempt on Sensitive Workflow
Trigger: Security telemetry flags suspicious activity against restricted systems.
First response: Contain exposure pathways, revoke risky sessions, and coordinate with designated response leadership.
Stabilization: Complete forensic review, remediate root controls, and update runbook actions from findings.
Third-Party Platform Incident Affecting Operations
Trigger: Vendor issue impacts a key operational workflow.
First response: Execute contingency routing, assign owner for vendor command path, and communicate operational impact.
Stabilization: Validate restoration quality, clear backlogs in controlled sequence, and refine fallback procedures.
Industry detail
Frequently asked questions
Plain-English answers for common buyer questions in this vertical.
Yes. We map controls and workflows to role-specific requirements and maintain documentation patterns that support operational accountability.
We sequence implementation phases around operational impact windows and prioritize continuity-first execution.
No. We strengthen your existing leadership model with implementation capacity, clearer ownership, and repeatable response operations.
Most agencies first see clearer incident command flow, faster triage coordination, and more consistent endpoint and access control execution.
Need a Law-Enforcement Support Path?
We scope a continuity-first delivery plan around your operational workflows, access model, and incident readiness priorities.