Local retail operators with checkout and inventory system dependencies
Retail IT & Security
Local Retail Shops
We help local retailers reduce checkout and inventory disruptions, improve endpoint and identity controls, and establish practical incident response discipline.

Industry detail
Ideal business profile
The kinds of teams and environments this page is built for.
Teams running lean staff models with limited in-house IT ownership
Businesses needing stronger controls around payment-adjacent workflows
Leaders prioritizing reliability improvements without excessive complexity
Industry detail
Operational environment
What day-to-day operations usually look like in this vertical.
Checkout flow reliability depends on endpoint, network, and payment integration stability
Inventory systems often integrate with ecommerce and supplier workflows
Store-level operations can vary by location, device, and staffing model
Endpoint drift and inconsistent access governance are common in fast-paced environments
Operational incidents can directly affect customer throughput and trust
Industry detail
Typical system dependencies
How daily work, handoffs, and technical dependencies usually line up.
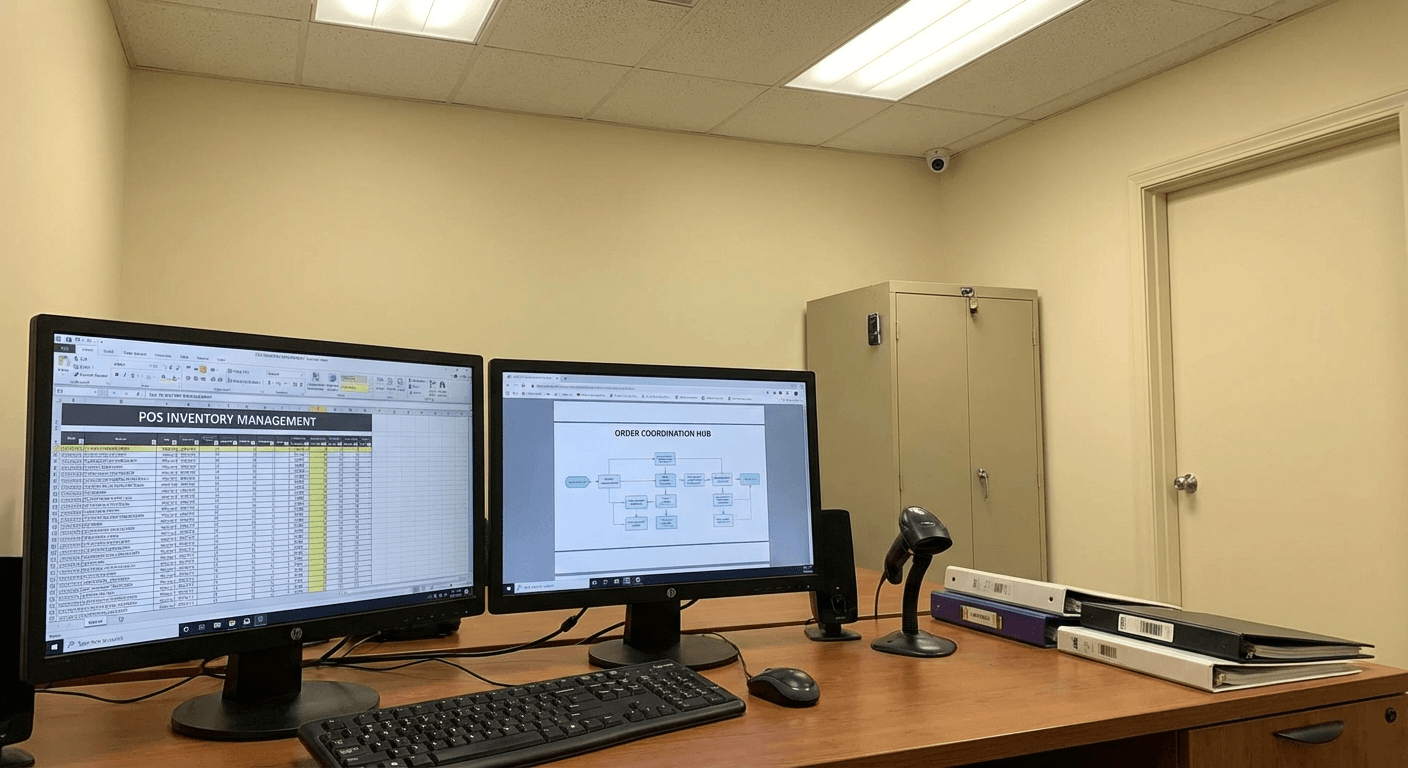
Systems and handoffs that shape support priorities
Use this view to connect technical recommendations to the way the team actually works.
Industry detail
Core pain points
The recurring issues that usually create stress, exposure, or operational drag.
Checkout interruptions during business hours
Inventory system lag or synchronization inconsistencies
Inconsistent endpoint hardening across store devices
Escalation delays for payment or POS integration incidents
Limited capacity for proactive risk and continuity improvements
Industry detail
Risk realities
Where threats and fragility tend to concentrate for this type of organization.
Payment and checkout disruption has immediate revenue and customer-experience impact
Weak segmentation and access controls increase avoidable security exposure
Inventory inaccuracies amplify operational inefficiency and customer friction
Unclear response ownership lengthens recovery windows
Industry detail
Compliance context
Frameworks and regulatory obligations that shape priorities in this sector.
PCI DSS
Retail payment workflows require disciplined controls around cardholder-data pathways.
How Blueforce applies it: We reduce payment-adjacent exposure with segmentation, endpoint governance, and operational safeguards.
FTC Data Security Expectations
Retail businesses are expected to use reasonable safeguards and execute incident response effectively.
How Blueforce applies it: We implement practical controls and role-owned response workflows that teams can execute consistently.
CISA SMB Cyber Baselines
Core controls and readiness practices reduce disruption for local operators with limited resources.
How Blueforce applies it: We sequence improvements by highest operational impact and execution feasibility.
Industry detail
Service mapping
How Blueforce services map into the actual needs of this environment.
Primary track
Managed IT & Cybersecurity Foundation
Strengthen store-level reliability and reduce security exposure in checkout and inventory pathways.
- • Support model for rapid checkout-impact incident triage
- • Endpoint and network hardening for store operations
- • Access-control governance for payment and inventory systems
- • Documented incident runbooks for POS and inventory disruptions
Expansion track
AI & Context Operations Expansion
Improve internal throughput for repetitive coordination tasks once core operations are stable.
- • Context-aware triage and routing for support tickets
- • Automation of repetitive inventory and status coordination workflows
- • Operational dashboards for trend-based issue detection
- • Governance and quality checks for safe automation rollout
Industry detail
30 / 60 / 90 roadmap
A practical phased sequence for stabilizing the environment.
Days 1-30
Stabilize checkout-critical and inventory-critical dependencies.
- • Map checkout and inventory dependency chain with owners
- • Define incident severity and escalation communication protocol
- • Close highest-risk access and endpoint weaknesses
- • Establish visibility reporting for store operations leadership
Days 31-60
Normalize control execution and incident response quality.
- • Standardize remediation and exception handling
- • Refine access boundaries for payment-adjacent workflows
- • Run disruption drills for checkout and inventory incidents
- • Improve vendor escalation path clarity and execution
Days 61-90
Scale predictable store operations and resilience.
- • Tune support handoffs and routing accuracy
- • Introduce targeted automation for repetitive operational tasks
- • Formalize recurring risk and continuity review cadence
- • Refresh roadmap from observed support and incident patterns
Industry detail
Priority support path
The work needs clear ownership, timing, and follow-through.
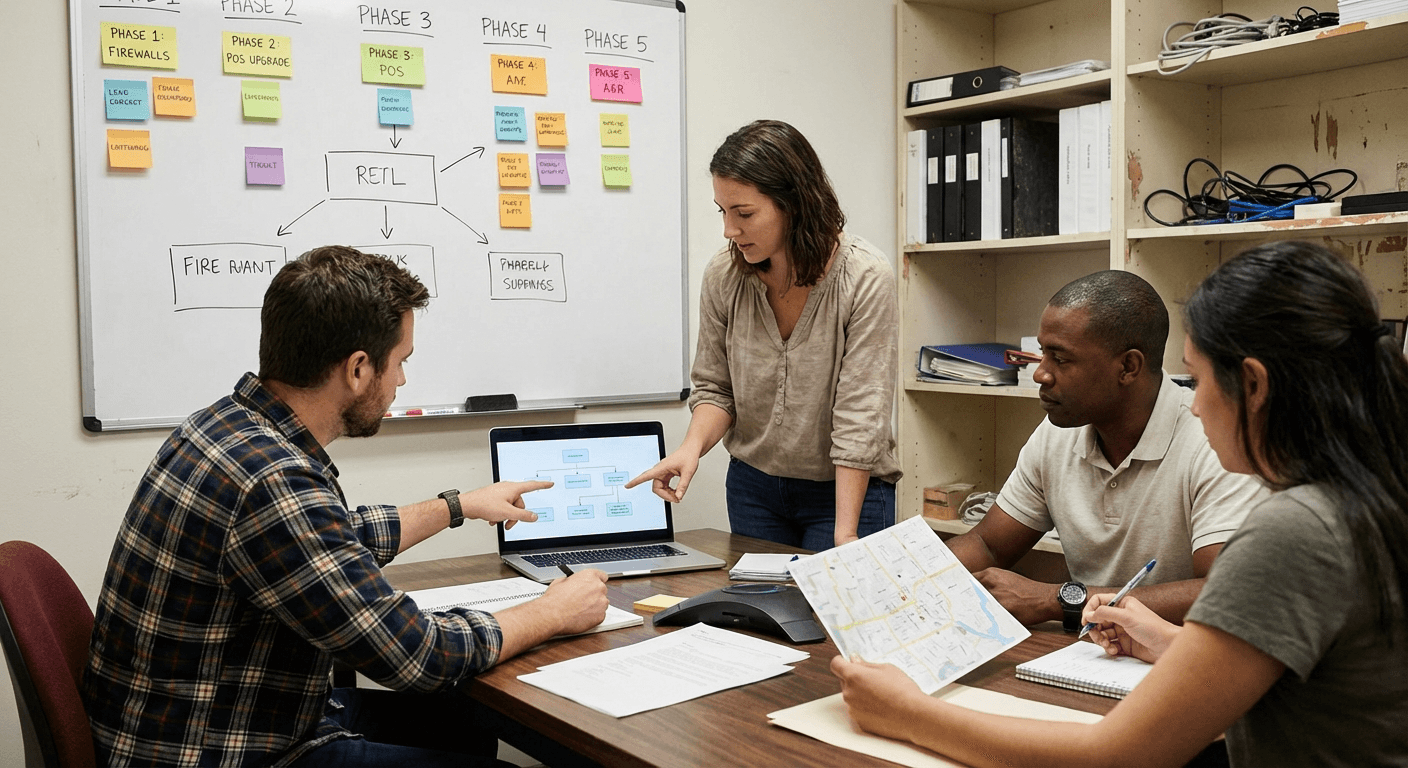
Support rhythm that matches the team
Each phase needs ownership, sequencing, and a support model that fits the way work gets done.
Industry detail
Priority controls checklist
The controls and process disciplines most often worth addressing first.
Map payment, checkout, and inventory dependencies by impact
Enforce role-based access and credential hygiene across store teams
Standardize endpoint posture across all operational devices
Document continuity procedures for checkout disruptions
Track high-risk remediation backlog and aging
Validate recovery procedures and owner assignments
Define vendor escalation expectations and timelines
Review incident trends with leadership on a fixed cadence
Industry detail
Scenario playbooks
Examples of the kinds of situations this environment needs to be ready for.
Checkout Service Disruption During Store Hours
Trigger: POS instability causes prolonged transaction delays.
First response: Route high-priority support path, enforce continuity operating procedure, and communicate queue-handling guidance.
Stabilization: Restore checkout flow, reconcile impacted transactions, and tighten recurrence controls.
Inventory Synchronization Failure
Trigger: Inventory data mismatch causes stock and fulfillment confusion.
First response: Contain affected sync pathways, assign incident owner, and switch to controlled fallback process.
Stabilization: Reconcile inventory records, validate integration health, and improve monitoring thresholds.
Suspicious Account Activity in Store Systems
Trigger: Security telemetry indicates potential unauthorized access.
First response: Contain account scope, revoke active risk sessions, and execute incident notification path.
Stabilization: Complete remediation actions and update access governance and detection workflows.
Industry detail
Frequently asked questions
Plain-English answers for common buyer questions in this vertical.
Yes. We sequence implementation around store realities and prioritize practical controls that reduce daily operational friction.
Usually no. We first improve stability and control execution around your current stack, then evaluate replacement only when justified.
We phase work around operating windows, prioritize high-impact fixes first, and maintain clear continuity procedures during changes.
Most retailers first see faster incident routing, improved checkout reliability, and stronger consistency in endpoint and access controls.
Need a Retail Support Path?
Get a scoped plan aligned to checkout continuity, inventory reliability, and practical risk reduction.