Nonprofit organizations with lean internal IT ownership
Nonprofit IT & Security
Nonprofits
We help nonprofit teams stabilize day-to-day operations, protect sensitive stakeholder data, and implement technology improvements in phases that match internal capacity.

Industry detail
Ideal business profile
The kinds of teams and environments this page is built for.
Teams handling donor, member, beneficiary, or program-sensitive data
Operations that depend on a small set of critical systems and integrations
Leadership seeking practical implementation tied to mission outcomes
Industry detail
Operational environment
What day-to-day operations usually look like in this vertical.
Program delivery, fundraising, and operations often share overlapping tooling
Small teams handle broad responsibilities with limited specialized capacity
Endpoint and identity controls vary across full-time, part-time, and volunteer usage
Vendor platforms are common but not always integrated with consistent governance
Reactive support cycles can crowd out strategic resilience work
Industry detail
Typical system dependencies
How daily work, handoffs, and technical dependencies usually line up.
Systems and handoffs that shape support priorities
Use this view to connect technical recommendations to the way the team actually works.
Industry detail
Core pain points
The recurring issues that usually create stress, exposure, or operational drag.
Limited internal bandwidth for proactive security and operational maintenance
Inconsistent controls around sensitive donor and stakeholder information
Operational disruptions that directly impact program delivery
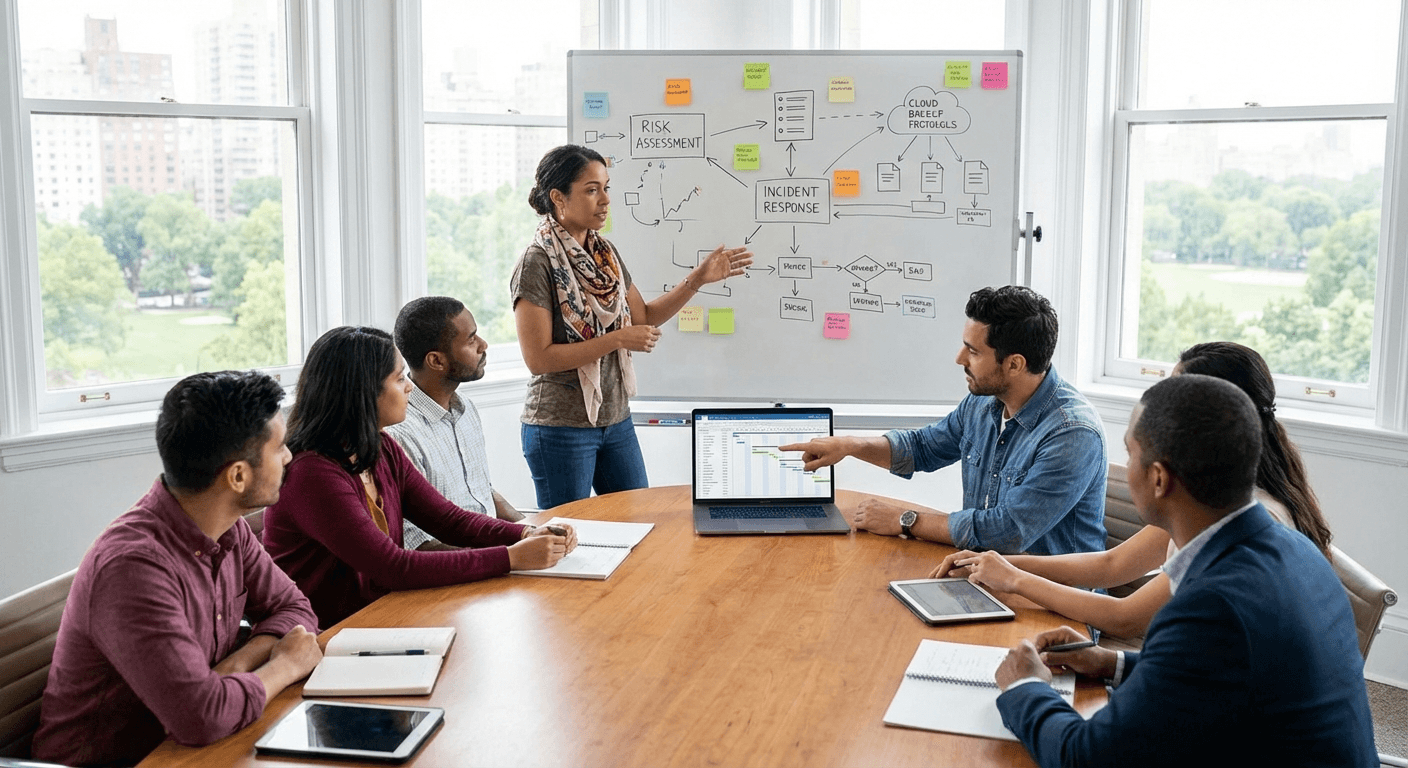
Weak escalation clarity during multi-system incidents
Technology priorities competing with mission and budget constraints
Industry detail
Risk realities
Where threats and fragility tend to concentrate for this type of organization.
Resource constraints can delay remediation of known high-impact risks
Access governance complexity increases with mixed staffing models
Incident response quality suffers when runbooks and ownership are unclear
Dependency on third-party tooling can create hidden continuity risk
Industry detail
Compliance context
Frameworks and regulatory obligations that shape priorities in this sector.
NIST SP 1300 (SMB Cybersecurity Guide)
Practical baseline practices support smaller organizations, including nonprofits, in building sustainable security operations.
How Blueforce applies it: We prioritize controls that deliver meaningful risk reduction with manageable operational overhead.
CISA Cyber Performance Goals
Core cyber outcomes should be practical, measurable, and continuously maintained.
How Blueforce applies it: We implement phased control improvements with clear ownership and recurring validation.
Data Stewardship Expectations
Nonprofits are expected by stakeholders to protect sensitive information with credible operational safeguards.
How Blueforce applies it: We build defensible access, endpoint, and response discipline aligned to trust and stewardship needs.
Industry detail
Service mapping
How Blueforce services map into the actual needs of this environment.
Primary track
Managed IT & Cybersecurity Foundation
Create stable mission operations and improve security posture without overburdening lean internal teams.
- • Support model tuned for mission-critical workflow uptime
- • Endpoint and identity baseline controls with practical governance
- • Risk-prioritized remediation cadence with ownership clarity
- • Incident response playbooks aligned to team capacity
Expansion track
AI & Context Operations Expansion
Once stable, improve throughput for repetitive admin and coordination workflows.
- • Context-aware queue triage for support and operations requests
- • Automation of repetitive internal and stakeholder-facing updates
- • Operational telemetry for backlog, response quality, and trend tracking
- • Governance checkpoints for safe and sustainable AI usage
Industry detail
30 / 60 / 90 roadmap
A practical phased sequence for stabilizing the environment.
Days 1-30
Stabilize mission-critical systems and clarify ownership.
- • Map critical program and fundraising workflow dependencies
- • Define escalation ownership and communication standards
- • Address top access and endpoint control risks
- • Establish leadership-visible operational status reporting
Days 31-60
Normalize security and support execution discipline.
- • Standardize remediation and exception workflows
- • Implement role-aligned access and identity refinements
- • Run scenario drills for service and security incidents
- • Improve third-party coordination protocols
Days 61-90
Scale reliability and resource-efficient operations.
- • Tune support routing and handoff consistency
- • Deploy targeted automation for repetitive coordination tasks
- • Formalize recurring posture and readiness reviews
- • Refresh roadmap from real support and incident patterns
Industry detail
Priority support path
The work needs clear ownership, timing, and follow-through.
Support rhythm that matches the team
Each phase needs ownership, sequencing, and a support model that fits the way work gets done.
Industry detail
Priority controls checklist
The controls and process disciplines most often worth addressing first.
Identify mission-critical systems and dependency owners
Enforce baseline access controls for sensitive stakeholder data
Standardize endpoint and patching governance
Document escalation and communication ownership
Track unresolved high-risk remediation work
Validate recovery procedures and backup accountability
Harden third-party integration and access pathways
Review risk and continuity status with leadership regularly
Industry detail
Scenario playbooks
Examples of the kinds of situations this environment needs to be ready for.
Fundraising Workflow Platform Outage
Trigger: Core fundraising or donor-management system becomes unavailable.
First response: Activate continuity workflow, route priority escalation, and communicate operational impact to stakeholders.
Stabilization: Restore service, reconcile pending transactions or records, and harden fallback procedures.
Suspicious Access Activity in Stakeholder Data Tools
Trigger: Authentication anomalies indicate possible misuse of privileged credentials.
First response: Contain account scope, validate affected systems, and execute incident communication protocol.
Stabilization: Complete remediation, strengthen controls, and update runbooks with lessons learned.
Program Operations Coordination Breakdown
Trigger: Cross-team tools and handoffs fail, delaying mission-critical delivery.
First response: Assign incident owner, stabilize the highest-impact workflow first, and apply temporary routing controls.
Stabilization: Normalize operations, remove bottlenecks, and formalize improved handoff governance.
Industry detail
Frequently asked questions
Plain-English answers for common buyer questions in this vertical.
Yes. We design implementation scope around realistic team capacity and prioritize operational wins that reduce daily firefighting.
We map technical priorities to mission-critical workflows and sequence changes by delivery impact and risk reduction.
Usually no. We start by strengthening controls and workflows around your current tools, then recommend replacements only when necessary.
Most nonprofits first see better incident ownership, fewer repeated support issues, and more consistent control execution.
Need a Nonprofit Support Path?
Get a scoped delivery path that matches your mission priorities, staffing capacity, and risk profile.